Cyber Security in Cloud Computing & Virtualization Course
Data Security in the Cloud. How Secure Is It?
Cloud security encompasses various technologies, services, and practices that protect cloud data, applications, and infrastructure from cyber risks. Strong cloud cybersecurity is essential to prevent data loss and ensure the privacy of data.
Cloud cybersecurity is provided by Cloud Service Providers (CSPs) or by the customers themselves. CSPs typically offer advanced security technology and safeguard customers from known and potential threats alike.
"Cyber Security in Cloud Computing and Virtualization" is a course that focuses on information security, virtualization systems, and cloud computing. Cloud computing refers to remote technology service providers via the internet, such as data storage and application deployment using internet resources, leveraging technologies like virtualization and cloud computing.
The course covers a variety of topics related to cybersecurity in cloud and virtualization environments, including:
- Cloud Security: How to protect data stored in the cloud environment, including access protection, user authentication, defense against cyber threats, and privacy protection.
- Virtual Machine Security: Protecting virtual machines; virtualization, authentication, sensitive data management within virtual machines, and detection of attacks.
- Network and Communication Security: How to secure communication between virtual machines and cloud systems, including defense against breaches, protection from DoS attacks, and identification of attacks.
- Access Management: How to manage user permissions in cloud and virtualization environments, including identity management, authentication, and protection of user accounts.
- Data Security: Protecting sensitive data stored in cloud and virtualization environments, including advice on guarding against data theft and malicious use.
- Threats and Attacks: Understanding cyber attacks that may affect cloud and virtualization environments, including types of attacks, potential damages, and how to deal with them.
The course provides students with a deep understanding of the unique cybersecurity challenges in cloud computing and virtualization, and equips them with the knowledge and tools necessary to defend and monitor information systems and infrastructure using advanced security.


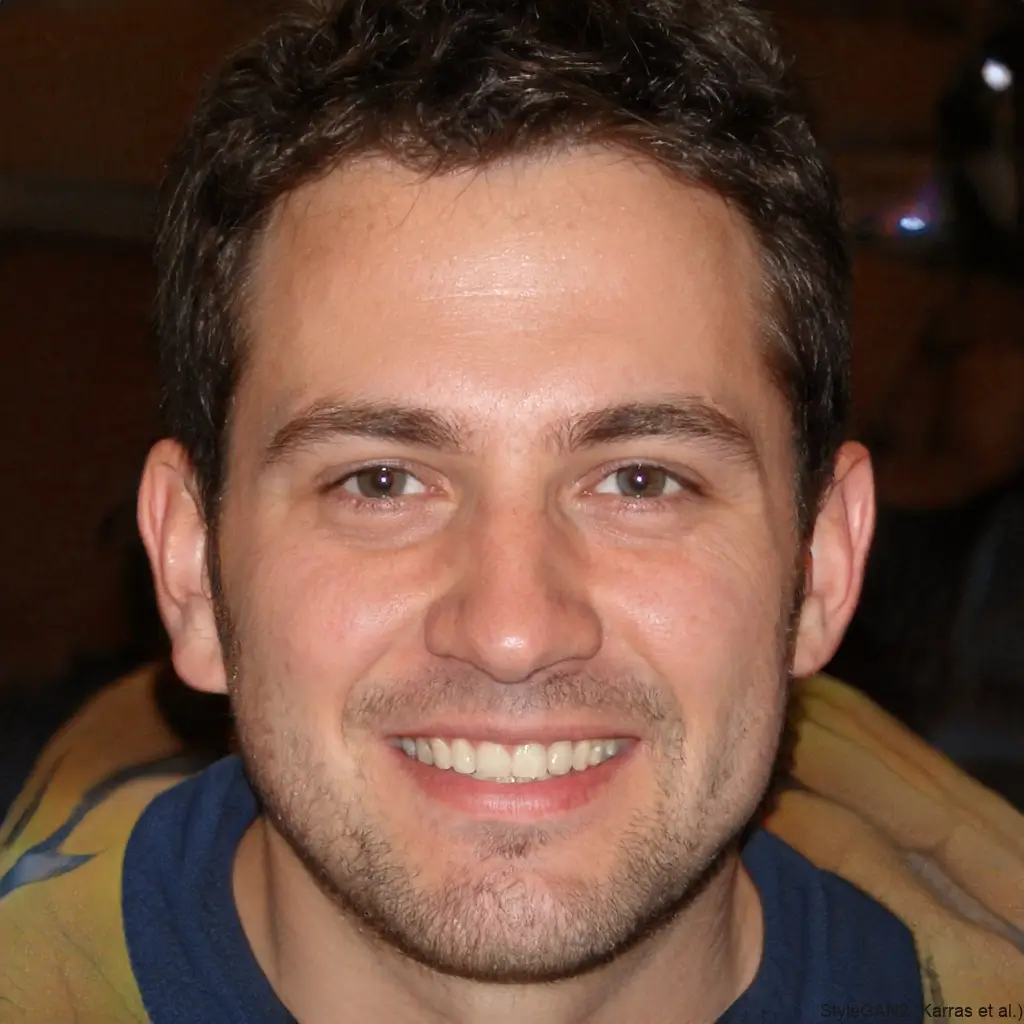
Meet your instructor
Benny Cohen
Embedded Academy Founder and CEO
As a long-time veteran in the technology industry, Benny Cohen combines a deep passion for technology with extensive field experience. With a B.Sc. in Electronics Engineering and an M.Sc. in Communication Engineering, he has spent over 20 years developing software and hardware systems, including the last few years focusing on the cybersecurity industry. In addition to his role as the company founder & CEO, Benny also operates as a hands-on practitioner who specializes in penetration testing and has conducted significant security assessments for leading enterprises and security companies worldwide. His approachable teaching style and real-world expertise make learning both engaging and relevant.
What our graduates say
Our graduates work here
Blog
News, insights, and learning resources from Embedded Academy


.webp)
.webp)